Traditionally, the primary focus in software development has been functionality. While numerous methodologies exist to facilitate this, they often overlook security as a crucial component. Yet addressing software issues during the maintenance stage is typically costly and complex. While resolving faults during the design stage can take time initially, it significantly reduces work and code modifications later on. An IBM System Science Institute study revealed that fixing a fault during maintenance can cost up to 100 times more than during the design phase.
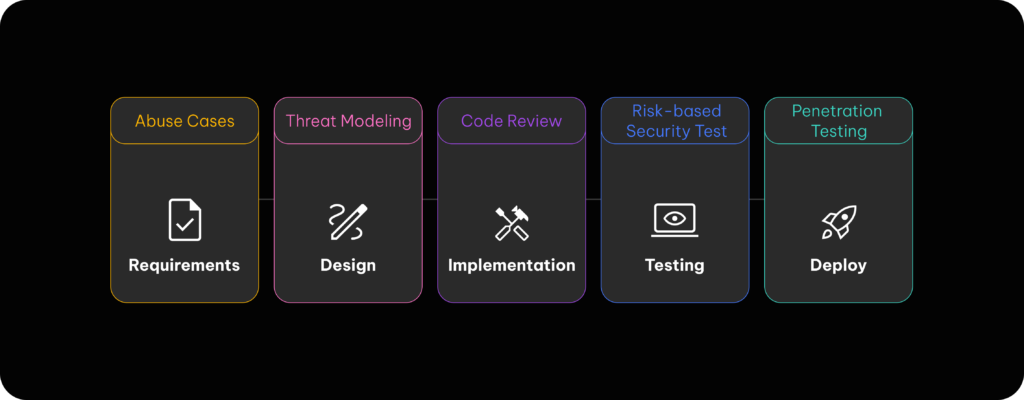
To find a better solution and approach, a “secure development cycle” has been adopted by many organizations, which integrates security principles into all stages of development. For example, threat modeling can be included during the design phase to establish security requirements and perform security tests alongside functional tests.
There are three key reasons why it is necessary to prioritize security in software development:
- Proactive protection. Integrating security from the start identifies and addresses vulnerabilities before exploitation. This proactive approach mitigates risks from the outset.
- Alignment with Agile development principles. Incorporating security practices into the development lifecycle aligns with Agile principles, enabling faster and safer deliveries. Security is not a hindrance to development, but rather a facilitator for robust and reliable products.
- Reputation and customer trust. Security is key in maintaining customer trust. Users expect their data to be safe, and applications to be resilient to threats. Early security investment aids in building a solid, enduring reputation.
Qubika offers services to protect your digital assets, including:
- Secure software development lifecycle. We guide our teams from design to implementation, ensuring a comprehensive approach at every software lifecycle stage. These services include:
- Threat modeling
- Static code analysis
- Penetration testing
- Continuous vulnerability scanning. We use advanced tools for continuous code scans and security assessments, identifying and rectifying vulnerabilities in real time.
- Incident response. If a security incident occurs, our response team takes immediate action to contain, investigate, and mitigate the threat, ensuring minimal disruption and protecting your systems’ integrity.
Conclusion
In summary, integrating security principles throughout the software development lifecycle is crucial. It not only allows for the early identification and mitigation of vulnerabilities while facilitating faster, safer deliveries, but it also helps maintain customer trust and a strong, reliable reputation.
Qubika’s comprehensive cybersecurity services, that include implementing secure software development lifecycles, continuous monitoring, and incident response, have been specifically designed to ensure the integrity of enterprise systems.
For more information, please visit our Cloud, SRE & Cybersecurity Studio webpage.